IT Solutions Experts
Providing comprehensive IT, SAP ERP, S/4 HANA, and cybersecurity support and training in Chicago.
IT Solutions
Providing comprehensive IT and cybersecurity solutions for businesses.
ERP Training
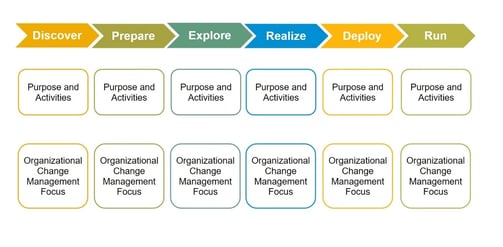
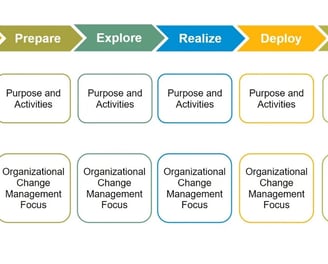
iMake solutions is an strategic Partners for Manufacturing , Distribution and Retail Clients. From SAP implementation and system integration to process optimization and cloud migration, our services cover the entire spectrum of SAP solutions. We also provide ongoing support, training, and maintenance to ensure your SAP environment operates very effectively.


Cybersecurity Support
Expert cybersecurity support to safeguard your business from threats.
Network Security:
· Firewalls: Implement and maintain firewalls to monitor and control network traffic, blocking unauthorized access.
· Intrusion Detection/Prevention Systems (IDS/IPS): Deploy IDS/IPS to detect and prevent malicious activity on the network.
· Network Segmentation: Segment the network to isolate critical systems and data, limiting the potential impact of a breach.
· Vulnerability Scanning: Regularly scan the network for vulnerabilities and address them promptly.
· Endpoint Security
· Antivirus/Anti-Malware Software: Install and maintain up-to-date antivirus and anti-malware software on all endpoints.
· Endpoint Detection and Response (EDR): Implement EDR solutions to detect and respond to advanced threats on endpoints.
· Device Security: Implement security measures on all devices, including mobile devices, to prevent unauthorized access and data breaches.
· Data Security
· Data Encryption: Encrypt sensitive data both in transit and at rest to protect it from unauthorized access.
· Data Loss Prevention (DLP): Implement DLP solutions to prevent sensitive data from leaving the organization's control.
· Data Backup and Recovery: Regularly back up critical data and implement a robust disaster recovery plan.




· Cloud Security
· Cloud Security Assessment: Assess the security posture of cloud environments and implement appropriate security controls.
· Cloud Access Security Broker (CASB): Use CASB solutions to monitor and control access to cloud applications.
· Cloud Data Security: Implement data encryption and other security measures to protect data stored in the cloud.


Email Security:
· Email Security Gateway: Implement an email security gateway to filter out spam and malicious emails.
· Phishing Awareness Training: Conduct regular phishing awareness training to educate employees about phishing attacks.
· Email Authentication: Implement email authentication protocols to prevent spoofing and phishing.
Ongoing Security Measures:
Incident Response Plan: Develop and maintain a comprehensive incident response plan to address security incidents effectively.
Security Monitoring: Continuously monitor security systems and logs for suspicious activity.
Threat Intelligence: Stay informed about the latest cyber threats and vulnerabilities.
Regular Security Updates: Keep all software and systems up to date with the latest security patches.
Review and Update Security Measures: Regularly review and update security policies and procedures to address evolving threats.





Solutions
Expert IT, SAP ERP, S/4 HANA, and cybersecurity training services.










imake Solutions
Expert IT , ERP, S/4 Hana and cybersecurity services for businesses.
Training
Support
Care@imakesolution.com
whatsapp+12246058693
© 2025. All rights reserved.
